Describe The Security Risks Associated With Software

So, we all love our shiny new gadgets, right? The phones that do everything but walk the dog, the laptops that can probably write a novel if we asked them nicely, and the smart fridges that judge our midnight snack choices. It's a digital wonderland! But here's a little secret, whispered from the shadowy corners of the internet: all this amazing software, the stuff that makes our lives super convenient, also comes with its own little bag of tricks. And not the fun kind, like a magician pulling a rabbit out of a hat. These are more like the tricks where a gremlin sneaks into your car and messes with the radio when you're late for work.
Let's talk about software security risks. Sounds a bit dry, doesn't it? Like watching paint dry while listening to a lecture on tax law. But stick with me! It's actually pretty fascinating, in a "oh-dear-I-should-probably-do-something-about-that" kind of way. Imagine your software is like a really fancy house. It's got great Wi-Fi, a killer entertainment system, and probably a self-cleaning oven. But then there are the tiny cracks in the foundation, the slightly loose window latch, the back door that you sometimes forget to lock properly. These are the vulnerabilities. They are the digital equivalent of leaving your spare key under a fake rock for everyone to find.
One of the most common troublemakers is something called malware. Think of malware as digital pests. We've got viruses that love to spread and mess things up, like that really annoying cold that goes around the office. Then there are worms, which are like viruses but can actually travel on their own. No need to attach themselves to another program; they’re independent little troublemakers. And let's not forget Trojans. These are the sneaky ones. They pretend to be something helpful, like a free game or a useful app, but BAM! Once you let them in, they’re up to no good, probably stealing your login details or turning your computer into a zombie, which, let's be honest, sounds like a terrible roommate.
Must Read
Then we have phishing. Oh, phishing. This is where the bad guys try to trick you into giving them your sensitive information. They send you emails that look exactly like they came from your bank, or your favorite online store, or even your boss. They'll say something urgent, like "Your account has been compromised! Click here immediately to reset your password!" And you, in your rush to save your digital kingdom, click that link. But that link doesn't take you to a password reset page; it takes you to a fake website designed to steal your username and password. It’s like someone dressing up as a police officer to get you to hand over your wallet. Not cool, digital bandits, not cool at all.
And what about ransomware? This one is particularly nasty. It’s like a digital kidnapper. They lock up all your important files, your precious photos, your work documents, and then demand a ransom in cryptocurrency to unlock them. Imagine your entire computer screen turning red with a demand for money. It’s enough to make you want to go live in a cabin in the woods with no internet, isn't it? Though, even then, a squirrel might chew through your ethernet cable if you had one.

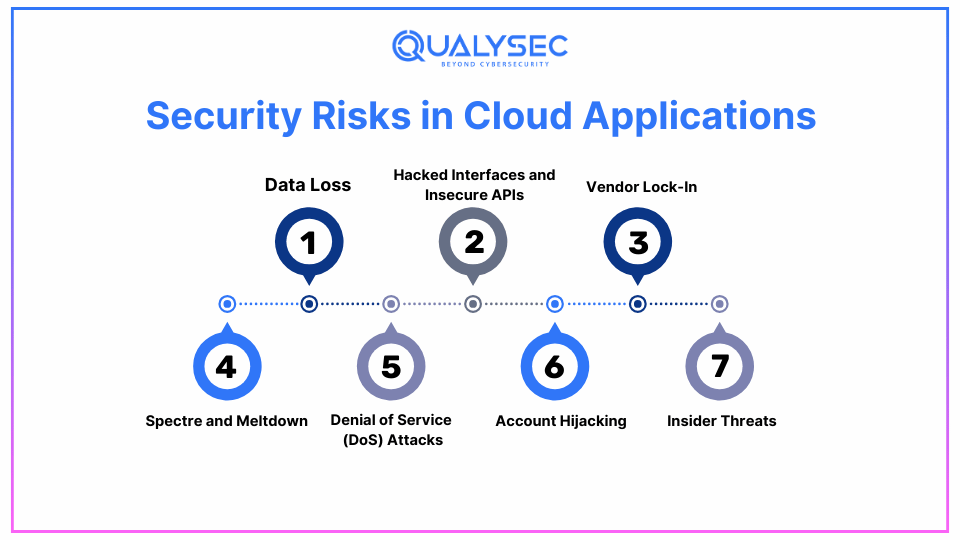
We also have to worry about insider threats. This isn't always malicious, but sometimes someone with legitimate access to a system decides to do something they shouldn't. Maybe it's an unhappy employee, or someone who made a mistake. It's like the friendly neighbor who has a spare key to your house suddenly deciding to borrow your fancy lawnmower and… forget to return it. Or worse.
Unpatched software is another biggie. Developers are constantly finding bugs and security holes in their software and releasing updates to fix them. But many of us, myself included, are guilty of clicking "Remind me later" when that update notification pops up. It’s like knowing there’s a tiny hole in your roof but deciding to deal with it after the next rainstorm. Eventually, that tiny hole can become a giant leak. These updates are like the digital equivalent of patching up those cracks in the foundation before a hurricane hits.
It’s easy to think, "Oh, this won't happen to me." But the reality is, we're all connected. Our personal devices, our work computers, even our smart toasters are all potential entry points for trouble.
Then there are data breaches. This is when hackers manage to get into a company's systems and steal massive amounts of user data. Think about all the places you've signed up online. If one of those companies has a data breach, your name, address, email, and sometimes even your credit card information could end up in the wrong hands. It’s like leaving your address book open on a park bench.
And let's not forget the simple, yet surprisingly effective, weak passwords. We all do it. We use "password123," or our pet's name, or our birthday. Hackers have tools that can guess these passwords in seconds. It’s like leaving your front door wide open with a sign that says, "Hello, please come in and take whatever you like!"
So, while we're enjoying the wonders of modern technology, it's good to remember that there are folks out there who want to exploit these digital cracks. It’s not about being paranoid; it's about being aware. It’s like knowing where the bear traps are when you’re hiking in the woods. You don't expect to step on one, but knowing they exist means you're more likely to watch where you're going. And maybe, just maybe, that unpopular opinion is that our software is a little like a beautiful, but slightly leaky, ship sailing on a vast, and sometimes choppy, digital ocean.